Website Hacking Tools For Mac
Table of Contents
Using our clues to track down the hacker Now that you know the potential hackers IP address, you can use that to track them down. The first thing you want to do is get a general geographical. Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site it can detect the injection and exploit it, either by using the union technique or a Boolean query based technique. The Mole uses a command based interface, allowing the user to indicate the action he wants to perform easily.
Introduction
Have you ever been connected to your computer when something strange happens? A CD drive opens on its own, your mouse moves by itself, programs close without any errors, or your printer starts printing out of nowhere? When this happens, one of the first thoughts that may pop into your head is that someone has hacked your computer and is playing around with you. Then you start feeling anger tinged with a bit of fear, because someone is violating your personal space without your permission and potentially accessing your private data. At these times instead of panicking, this tutorial will show what to do and how to potentially help you track down the hacker and report them to the authorities.
When your computer is hacked, a hacker will typically install a Remote Access Trojan, or RAT, that will allow them to gain access to it again in the future. This trojan will listen on a TCP or UDP port and wait for connections from the remote user. Once the remote user is connected they will have full access to your computer and be able to access files, programs, screen shots, and possibly your web cam.
While the hacker is connected, though, they are vulnerable because we can use programs that allow us to see the IP address that the user is connected from. This IP address can be used to find their approximate geographic location, possibly login names from their computer, and identity clues from their host names. We can then use this information to report them to the authorities or law enforcement. The first step is to proceed to the next section where you will learn how to use a tool called TCPView to examine the connections between your computer and a remote one.
Using TCPView in Windows to see who is connected to your computer
TCPView is a powerful tool for Windows that allows you to see all of the current TCP/IP network connections on your computer. As almost all remote hacks are perpetrated over the Internet, you will be able to use TCPView to quickly spot any remote computers that are connected to your computer. To use TCPView please download it from the following location and save it on your desktop:
To find a hacker that may be connected to your computer, run TCPView and accept the license agreement. You will now be shown a page that displays all of the active TCP/IP connections on your computer. If there is a remote user connected to your computer at this time, then TCPView will show their connection and the IP address they are connecting from.
When using TCPView always be sure to disable the resolve address feature as we want to see the connected IP addresses. To do this, when TCPView is open, click on the Options menu and then uncheck Resolve Addresses. Now that TCPView is setup properly, let's see how TCPView works by looking at a screen shot of TCPView showing only legitimate connections.
As you can see from the image above, the only programs that show an ESTABLISHED connection are related to the Internet Explorer process. If Internet Explorer was just used within the last 5-10 minutes, then these connections are legitimate connections that were made to various web sites. The processes that are in a LISTENING state look to be legitimate Windows programs, so they can be ignored as well. To be safe, though, you should always check the paths of all LISTENING programs by double-clicking on the program name. This will open a small dialog that shows you the path to the executable. If the program is in the proper place then you have confirmed that these are legitimate programs.
Now, let's say that you were using your computer and your CD drive ejected on its own. As this is a little strange you should start TCPView and look at its connections.
Can you spot the strange connection in the screen above? We see ESTABLISHED Internet Explorer connections to a variety of hosts, but if you recently used it then that is normal. At the very top, though, is a strange process called a.exe that has an established connection to to the remote IP address 67.83.7.212 and is listening on the local port number 26666. If you do not recognize the program or the remote address, then you should immediately become suspicious. The next step is to see if there is any legitimate program that uses that port number. By looking at this Wikipedia Page we see that there is no legitimate program assigned to the 26666 port number. If you are concerned that you are seeing a suspicious connection, you should definitely write down the name of the program, its file location, and the remote user's IP address so that you have it available later. You may also want to take screen shots in the event you need to show it to the authorities. Finally, we double-click on the process name to see where it is located and find that it is stored directly in the C:Program Files folder.
Executable programs should not be stored directly in the C:Program Files folder, so it paints a stronger case that this is not a legitimate program and that someone was accessing your computer without your permission. To be safe, you should end the process so that the hacker is no longer connected to the computer. Now that you know that someone has been accessing your computer without your permission, you should continue to the next section to learn how to use the information we just gathered to track them down.
Using our clues to track down the hacker
Now that you know the potential hackers IP address, you can use that to track them down. The first thing you want to do is get a general geographical location for the user. This can be done using the GeoIPTool site. When you are at that site, enter the IP address for the remote user you saw connected to your computer. GeoIPTool will then display the general location for this IP address as shown below.
As you can see from the above image, the remote IP address that connected to your computer is supposedly located in Clifton, New Jersey in the USA.
Unfortunately, the GeoIP information is not always accurate, so we want to use another tool called Traceroute to corroborate what the GeoIPTool showed. Traceroute is a program that will print out the host names of all the devices between your computer and the remote one. As ISPs typically give hosts names to their devices using geographical names, we can get further clues as to the location of the IP address.
To use Traceroute you can go to this web site: http://www.net.princeton.edu/traceroute.html. Once there, enter the hackers IP address and click on the Go button. A traceroute process can take a while, so you may want to do something for 5-10 minutes and then come back and check the results. When done, you should see output similar to what is shown below.
Notice the hostname of the last device in the traceroute and the portion that I highlighted. Based upon the information we received from GeoIPTool, this further confirms that the IP address most likely belongs to someone from Clifton, New Jersey.
In a real example, though, it will not always be as easy to figure out the location of a remote IP address. In those situations your best bet is to contact the abuse department for the ISP that owns the remote IP address and let them know what is going on. They will usually issue an alert to the hacker, which if nothing else, will scare them enough that maybe they wont do it again. To find out the name of the ISP that owns the particular IP address, you can go to http://whois.arin.net and enter the IP address in the Search Whois field in the top right of the home page. This will look up and list the Internet service provider that owns that particular IP address and will usually contain an email you can contact. If you plan on reporting this hack to the authorities, you should avoid contacting the ISP at this time.
Finally, someone accessing your computer without permission can be a federal crime, so if you are truly concerned, you can gather all of this information and contact your local police department's cyber crime division. If your police department does not have this division then you can contact the FBI Cyber Crime division.
What you should do once you know you have been hacked
Once you know you have been hacked you should immediately harden your computer's security so that it cannot happen again. To do this please perform each of these steps:
- Change all the passwords for all the accounts on your computer, your email accounts, and any banking accounts.
- Install all the available Windows Updates. Information on how to do this can be found in this tutorial: How to update Windows
- If you use Remote Desktop, change the port it listens on by using this tutorial: How to change the Terminal Services or Remote Desktop Port
- Check your programs for available updates using Secunia PSI: How to detect vulnerable and out-dated programs using Secunia Personal Software Inspector (PSI)
- Use a firewall on your network or your computer. The best line of defense from remote attacks is a hardware firewall such as a personal router. If you only have one computer and the Internet modem is connected directly to your computer, then make sure you enable the Windows firewall.
Once you have completed all of these steps, your computer will be much more secure.
Conclusion
Hopefully the information in this tutorial will help you to gain control of your computer in the event someone hacks it. When reviewing this information, though, it is important to not to jump to conclusions and assume every unknown established connection is a hacker. In most cases, connections you see in TCPView are all legitimate and nothing to be concerned about. If you do encounter something that looks suspicious to you, feel free ask us in the tech support forums. One of our members can help you determine if this connection is something that you really need to worry about.
Internet is now the basic need of our daily life. With the increasing use of smartphones, most of the things are now online. Every time we have to do something, we just use our smartphone or desktop. This is the reason wi-fi hotspots can be found everywhere.
People also use wireless in their home network to connect all devices. Every person can see the neighborhood wi-fi networks in the system, and they want to use it for free. But most these networks are secured with a password key. You need to know this security key to access the network. When your own network is down, you will desperately want to connect to these neighborhood networks. For this, people generally search for wi-fi password cracking tools to get unauthorized access to those wireless networks.
Sometimes when you are on a network, you also want to check what is happening on the network. This happens mostly in big organizations, when an employer wants to check who is doing what in the network. For these things, there are a few network hacking tools available that let users analyze packets and see what other users are doing.
In this article, I am going to discuss wireless security and best wi-fi password cracking or recovery tools. I will explain the kind of encryption wireless networks use and how these tools can crack the networks to get access. We will also see what tools let users monitor networks.
Wireless Networks and Hacking
Wireless networks are based on IEEE 802.11 standards defined by IEEE(Institute of Electrical and Electronics Engineers) for ad hoc networks or infrastructure networks. Infrastructure networks have one or more access points which coordinate the traffic between the nodes. But in ad hoc networks, there is no access point; each node connects in a peer-to-peer way.
Basically there are two types of vulnerabilities which can be found in the Wireless LAN. One is poor configuration and the other is poor encryption. Poor configuration is caused by the network admin who manages the network. It may include the weak password, no security settings, use of default configurations, and other user related things. Poor encryption is related to security keys used to protect the wireless network. It is there because of issues in WEP or WPA.
WEP and WPA
WEP and WPA are the two main security protocols used in Wi-Fi LAN. WEP is known as Wired Equivalent Privacy (WEP). It is a deprecated security protocol which was introduced back in 1997 as a part of original 802.11 standards. But it was weak, and several serious weakness were found in the protocol. Now, this can be cracked within minutes. So, a new kind of security protocol was introduced in 2003. This new protocol was Wi-Fi Protected Access (WPA). It has mainly two versions, 1 and 2 (WPA and WPA2). Now it is the current security protocol used in wireless networks. To get unauthorized access to a network, one needs to crack these security protocols. There are many tools which can crack Wi-Fi encryption. These tools can either take advantage of WEP weaknesses or use bruteforce attacks on WPA/WPA2. I am sure now you know that you should never use WEP security.
Basically wireless hacking tools are of two types. One of which can be used to sniff the network and monitor what is happening in the network. And other kinds of tools are used to hack WEP/WPA keys. These are the popular tools used for wireless password cracking and network troubleshooting.
1. Aircrack
Aircrack is one of the most popular wireless passwords cracking tools which you can use for 802.11a/b/g WEP and WPA cracking. Aircrack uses the best algorithms to recover wireless passwords by capturing packets. Once enough packets have been gathered, it tries to recover the password. To make the attack faster, it implements a standard FMS attack with some optimizations.
The company behind the tool also offers an online tutorial where you can learn how to install and use this tool to crack wireless passwords. It comes as Linux distribution, Live CD and VMware image options. You can use any of these. It supports most of the wireless adapters and is almost guaranteed to work. If you are using a Linux distribution, the only drawback of the tool is that it requires deeper knowledge of Linux. If you are not comfortable with Linux, you will find it hard to use this tool. In this case, try Live CD or VMWare image. VMWare Image needs less knowledge, but it only works with a limited set of host OS, and only USB devices are supported.
Before you start using this too, confirm that the wireless card can inject packets. Then start WEP cracking. Read the online tutorial on the website to know more about the tool. If you will follow steps properly, you will end up getting success with this tool.
Download: http://www.aircrack-ng.org/
2. AirSnort
AirSnort is another popular tool for decrypting WEP encryption on a wi-fi 802.11b network. It is a free tool and comes with Linux and Windows platforms. This tool is no longer maintained, but it is still available to download from Sourceforge. AirSnort works by passively monitoring transmissions and computing encryption keys once it has enough packets received. This tool is simple to use. If you are interested, you can try this tool to crack WEP passwords.
Download: http://sourceforge.net/projects/airsnort/
3. Cain & Abel
Cain & Abel is a popular password cracking tool. This tool is developed to intercept network traffic and then discover passwords by bruteforcing the password using cryptanalysis attack methods. It can also recover wireless network keys by analyzing routing protocols. It you are trying to learn wireless security and password cracking, you should once try this tool.
Download: http://www.oxid.it/cain.html
4. Kismet
Kismet is the wi-fi 802.11 a/b/g/n layer2 wireless network sniffer and IDS. It works with any wi-fi card which supports rfmon mode. It passively collects packets to identify networks and detect hidden networks. It is built on client/server modular architecture. It is available for Linux, OSX, Windows and BSD platforms.
Download: http://www.kismetwireless.net/
5. NetStumbler
NetStumbler is a popular Windows tool to find open wireless access points. This tool is free and is available for Windows. A trimmed down version of the tool is also available. It is called MiniStumbler.
Basically NetStumblet is used for wardriving, verifying network configurations, finding locations with a poor network, detecting unauthorized access points, and more.
But the tool also has a big disadvantage. It can be easily detected by most of the wireless intrusion detection systems available. This is because it actively probes a network to collect useful information. Another disadvantage of the tool is that it does not work properly with the latest 64 bit Windows OS. This is because the tool was last updated back in April 2004. It has been around 11 years since the last stable release of the tool.
Download Netstumbler: http://www.stumbler.net/
6. inSSIDer
inSSIDer is a popular Wi-Fi scanner for Microsoft Windows and OS X operating systems. Initially the tool was opensource. Later it became premium and now costs $19.99. It was also awarded as “Best Opensource Software in Networking”. The inSSIDer wi-fi scanner can do various tasks, including finding open wi-fi access points, tracking signal strength, and saving logs with GPS records.
Download inSSIDer: http://www.inssider.com/
7. WireShark
WireShark is the network protocol analyzer. It lets you check what is happening in your network. You can live capture packets and analyze them. It captures packets and lets you check data at the micro-level. It runs on Windows, Linux, OS X, Solaries, FreeBSD and others. WireShark requires good knowledge of network protocols to analyze the data obtained with the tool. If you do not have good knowledge of that, you may not find this tool interesting. So, try only if you are sure about your protocol knowledge.
Download Wireshark: https://www.wireshark.org/
8. CoWPAtty
CoWPAtty is an automated dictionary attack tool for WPA-PSK. It runs on Linux OS. This program has a command line interface and runs on a word-list that contains the password to use in the attack.
Using the tool is really simple, but it is slow. That’s because the hash uses SHA1 with a seed of SSID. It means the same password will have a different SSIM. So, you cannot simply use the rainbow table against all access points. So, the tool uses the password dictionary and generates the hack for each word contained in the dictionary by using the SSID.
The new version of the tool tried to improve the speed by using a pre-computed hash file. This pre-computed file contains around 172000 dictionary file for around 1000 most popular SSIs. But if your SSID is not in those 1000, you are unlucky.
Download CoWPAtty: http://sourceforge.net/projects/cowpatty/
9. Airjack
Airjack is a Wi-Fi 802.11 packet injection tool. This wireless cracking tool is very useful in injecting forged packets and making a network down by denial of service attack. This tool can also be used for a man in the middle attack in the network.
Download AirJack: http://sourceforge.net/projects/airjack/
10. WepAttack
WepAttack is an open source Linux tool for breaking 802.11 WEP keys. This tool performs an active dictionary attack by testing millions of words to find the working key. Only a working WLAN card is required to work with WepAttack.
Pc Hacking Tools
Download WebAttack: http://wepattack.sourceforge.net/
Windows 10 Hacking Tools
11. OmniPeek
OmniPeek is another nice packet sniffer and network analyzer tool. This tool is commercial and supports only Windows operating systems. This tool is used to capture and analyze wireless traffic. But it requires you to have good knowledge of protocols to properly understand things. A good thing is that the tool works with most of the network interface cards available in market. This tool is used for network troubleshooting. This tool also supports plugins, and 40 plugins are already available to extend the features of the tool.
Download: http://www.wildpackets.com/products/distributed_network_analysis/omnipeek_network_analyzer
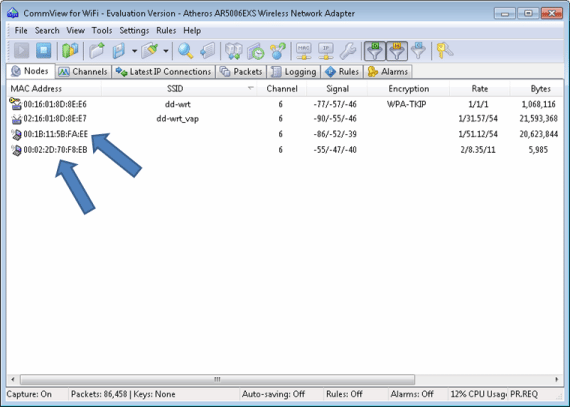
12. CommView for WiFi
CommView for WiFi is another popular wireless monitor and packet analyzer tool. It comes with an easy to understand GUI. It works fine with 802.11 a/b/g/n/ac networks. It captures every packet and displays useful information as a list. You can get useful information like access points, stations, signal strength, network connections and protocol distribution.
Captured packets can be decrypted by user-defined WEP or WPA keys.
This tool is basically for wi-fi network admins, security professionals, and home users who want to monitor their wi-fi traffic and programmers working on software for wireless networks.
Download CommView: http://www.tamos.com/products/commwifi/
13. CloudCracker
CloudCracker is the online password cracking tool for cracking WPA protected wi-fi networks. This tool can also be used to crack different password hashes. Just upload the handshake file, enter the network name and start the tool. This tool has a huge dictionary of around 300 million words to perform attacks.
Try Cloudcracker: https://crack.sh/
Conclusion
In this post, I discussed 13 wireless hacking tools. A few wireless hacking tools are for cracking the password to get unauthorized access, and a few are for monitoring and troubleshooting the network. But most of the people really interested in tools to crack wireless hotspots just want to get free Internet access.
The above collection also contains those tools which try a dictionary attack to crack wi-fi passwords to allow you to get free Internet access. But be sure not to use these tools in a risky place. Hacking wireless networks to get unauthorized access may be a crime in your country. You may get into trouble for using these tools. So, please do not use these tools for illegal works. As I already mentioned, you should never use the WEP encryption key in your home or wireless network. With available tools, it is child’s play to crack the WEP keys and access your wi-fi network.
Wireless monitoring and troubleshooting tools are basically for network admins and programmers working on wi-fi based software. These tools really help when some of your systems face problems in connecting to the network.
I hope you enjoyed this article and got relevant information about popular wireless hacking and password cracking tools. I tried my best to compile this list of password hacking tools, but as a human error, I may miss something. If I forgot any important tool in this, please let me know in the comments.
